
Computers and Technology, 28.05.2021 01:10 volocibel
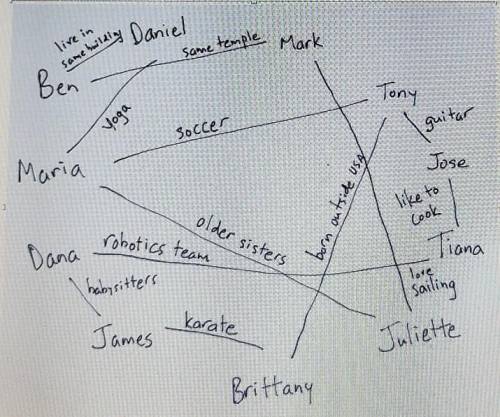
This picture shows some of the connections that students in a class have using these connections pick the most direct route you need to send a message from James to mark the message will first go to blank then the message should go to blank2 next to blank3 blank4 will get it next finally the message will go to mark

Answers: 2


Another question on Computers and Technology

Computers and Technology, 21.06.2019 18:30
Which number on the image above correctly indicates the name of a folder in this url? a.1b.2c.3d.4
Answers: 2

Computers and Technology, 22.06.2019 05:10
Read the code below. what will the computer print if the input for year_variable is 1700? if year_variable == 1776: print("your answer is correct. the declaration of independence was signed in “year_variable”.") elif year_variable < 1776: compute_variable = 1776 - year_variable. print("add “compute_variable“ years to your answer for the correct answer.") elif year_variable > 1776: compute_variable = year_variable - 1776 print("subtract “compute_variable” years from your answer for the correct answer.")
Answers: 1

Computers and Technology, 22.06.2019 10:50
A911 dispatcher is the sole sender of messages to all police officers. while on patrol, officers communicate with the dispatcher who, in turn, relays messages to other officers. the officers do not communicate directly with one another. this illustrates a network.
Answers: 1

Computers and Technology, 22.06.2019 12:50
You have just been hired as an information security engineer for a large, multi-international corporation. unfortunately, your company has suffered multiple security breaches that have threatened customers' trust in the fact that their confidential data and financial assets are private and secured. credit-card information was compromised by an attack that infiltrated the network through a vulnerable wireless connection within the organization. the other breach was an inside job where personal data was stolen because of weak access-control policies within the organization that allowed an unauthorized individual access to valuable data. your job is to develop a risk-management policy that addresses the two security breaches and how to mitigate these risks.requirementswrite a brief description of the case study. it requires two to three pages, based upon the apa style of writing. use transition words; a thesis statement; an introduction, body, and conclusion; and a reference page with at least two references. use a double-spaced, arial font, size 12.
Answers: 1
You know the right answer?
This picture shows some of the connections that students in a class have using these connections pic...
Questions


Mathematics, 06.05.2020 03:46


English, 06.05.2020 03:46


Arts, 06.05.2020 03:46


History, 06.05.2020 03:46

Mathematics, 06.05.2020 03:46


Mathematics, 06.05.2020 03:46

Mathematics, 06.05.2020 03:46

Chemistry, 06.05.2020 03:46

Computers and Technology, 06.05.2020 03:46

History, 06.05.2020 03:46


Mathematics, 06.05.2020 03:46

Chemistry, 06.05.2020 03:46

Mathematics, 06.05.2020 03:46

History, 06.05.2020 03:46



