
Computers and Technology, 14.12.2020 19:10 jackvj4959
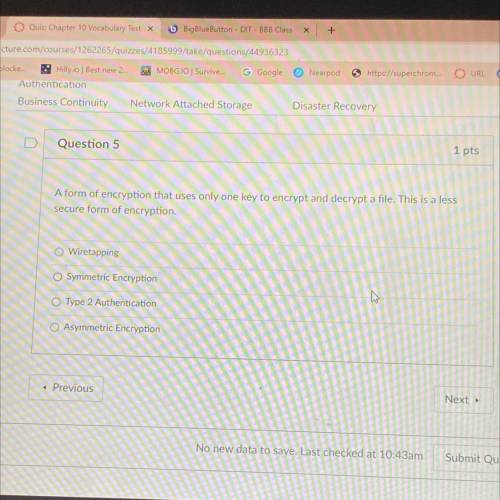
A form of encryption that uses only one key to encrypt and decrypt a file. This is a less
secure form of encryption
O Wiretapping
Symmetric Encryption
Type 2 Authentication
Asymmetric Encryption

Answers: 3


Another question on Computers and Technology

Computers and Technology, 22.06.2019 06:00
What are the most likely causes of conflict at the meeting? check all that apply.
Answers: 1

Computers and Technology, 22.06.2019 20:10
Assume that minutes is an int variable whose value is 0 or positive. write an expression whose value is "undercooked" or "soft-boiled" or "medium-boiled" or "hard-boiled" or "overcooked" based on the value of minutes. in particular: if the value of minutes is less than 2 the expression's value is "undercooked"; 2-4 would be a "soft-boiled", 5-7 would be "medium-boiled", 8-11 would be "hard-boiled" and 12 or more would be a "overcooked".
Answers: 1

Computers and Technology, 23.06.2019 20:00
What multimedia system creates an immersive, real-life experience that the user can interact with?
Answers: 1

Computers and Technology, 24.06.2019 00:20
The guy wire bd exerts on the telephone pole ac a force p directed along bd. knowing the p must have a 720-n component perpendicular to the pole ac, determine the magnitude of force p and its component along line ac.
Answers: 2
You know the right answer?
A form of encryption that uses only one key to encrypt and decrypt a file. This is a less
secure fo...
Questions

Business, 08.06.2021 20:50


Mathematics, 08.06.2021 20:50


Business, 08.06.2021 20:50


Mathematics, 08.06.2021 20:50



Mathematics, 08.06.2021 20:50







Chemistry, 08.06.2021 20:50


Biology, 08.06.2021 20:50



