Computers and Technology, 11.01.2021 16:10 brinjay430
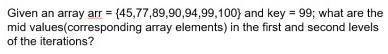
what are the array elements corresponding to the mid-avlues in the first and second iterations of a binary search in an array arr

Answers: 2


Another question on Computers and Technology

Computers and Technology, 22.06.2019 22:00
Discuss the ways in which electronic information associated with payments is addressed in terms of security. include encryption, secure sockets layers, and secure electronic transactions in your discussion. are there any other ways that consumers and businesses can keep their payment information secure in an electronic commerce environment? do you feel that your information is safe when conducting electronic business? why or why not?
Answers: 1

Computers and Technology, 23.06.2019 02:30
These factors limit the ability to attach files to e-mail messages. location of sender recipient's ability to open file size of file type of operating system used
Answers: 2

Computers and Technology, 23.06.2019 04:31
Q14 what is most important for you to choose before you build a network? a. private network b. nos c. network media d. network protocol e. directory service
Answers: 1

Computers and Technology, 24.06.2019 12:00
Jack is assisting his younger sibling mary with her mathematics assignment, which includes a study of the number system. jack explains to mary that whole numbers are counting numbers that could be used to record the number of fruits in a basket. which data type represents whole numbers? a.integers.b.floating-point numbers. c.strings.d.boolean
Answers: 1
You know the right answer?
what are the array elements corresponding to the mid-avlues in the first and second iterations of a...
Questions

History, 16.12.2020 14:00

Mathematics, 16.12.2020 14:00



Mathematics, 16.12.2020 14:00

Mathematics, 16.12.2020 14:00

Mathematics, 16.12.2020 14:00


English, 16.12.2020 14:00

Mathematics, 16.12.2020 14:00

Mathematics, 16.12.2020 14:00


Geography, 16.12.2020 14:00





Physics, 16.12.2020 14:00


English, 16.12.2020 14:00