
Computers and Technology, 16.12.2020 08:50 randyg0531
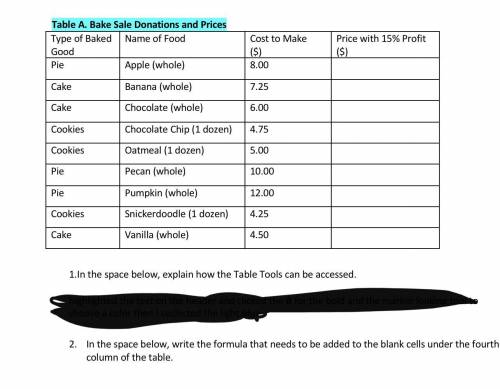
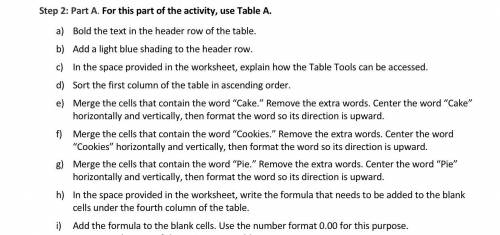
Step 2: Part A. For this part of the activity, use Table A. a) Bold the text in the header row of the table. b) Add a light blue shading to the header row. c) In the space provided in the worksheet, explain how the Table Tools can be accessed. d) Sort the first column of the table in ascending order. e) Merge the cells that contain the word “Cake.” Remove the extra words. Center the word “Cake” horizontally and vertically, then format the word so its direction is upward. f) Merge the cells that contain the word “Cookies.” Remove the extra words. Center the word “Cookies” horizontally and vertically, then format the word so its direction is upward. g) Merge the cells that contain the word “Pie.” Remove the extra words. Center the word “Pie” horizontally and vertically, then format the word so its direction is upward. h) In the space provided in the worksheet, write the formula that needs to be added to the blank cells under the fourth column of the table. i) Add the formula to the blank cells. Use the number format 0.00 for this purpose.

Answers: 2


Another question on Computers and Technology

Computers and Technology, 21.06.2019 16:10
Which is a benefit of peer-to-peer networking? easy to add or remove devices main server has a fast processor more reliable than a client/server network same software versions on all computers
Answers: 3

Computers and Technology, 22.06.2019 12:50
You have just been hired as an information security engineer for a large, multi-international corporation. unfortunately, your company has suffered multiple security breaches that have threatened customers' trust in the fact that their confidential data and financial assets are private and secured. credit-card information was compromised by an attack that infiltrated the network through a vulnerable wireless connection within the organization. the other breach was an inside job where personal data was stolen because of weak access-control policies within the organization that allowed an unauthorized individual access to valuable data. your job is to develop a risk-management policy that addresses the two security breaches and how to mitigate these risks.requirementswrite a brief description of the case study. it requires two to three pages, based upon the apa style of writing. use transition words; a thesis statement; an introduction, body, and conclusion; and a reference page with at least two references. use a double-spaced, arial font, size 12.
Answers: 1

Computers and Technology, 22.06.2019 17:00
Annie is creating a corporate report for a company’s annual meeting. in the report, she wants to add the signature of various department heads. which device can annie use to capture signatures to include in the report? a. printer b. monitor c. e-reader d. digitizing tablet
Answers: 1

Computers and Technology, 23.06.2019 15:30
The processing of data in a computer involves the interplay between its various hardware components.
Answers: 1
You know the right answer?
Step 2: Part A. For this part of the activity, use Table A. a) Bold the text in the header row of th...
Questions


Mathematics, 22.04.2021 19:20



Spanish, 22.04.2021 19:20



Mathematics, 22.04.2021 19:20

Mathematics, 22.04.2021 19:20

English, 22.04.2021 19:20

Business, 22.04.2021 19:20




English, 22.04.2021 19:20


Mathematics, 22.04.2021 19:20





