Computers and Technology, 07.04.2020 23:14 crosales102
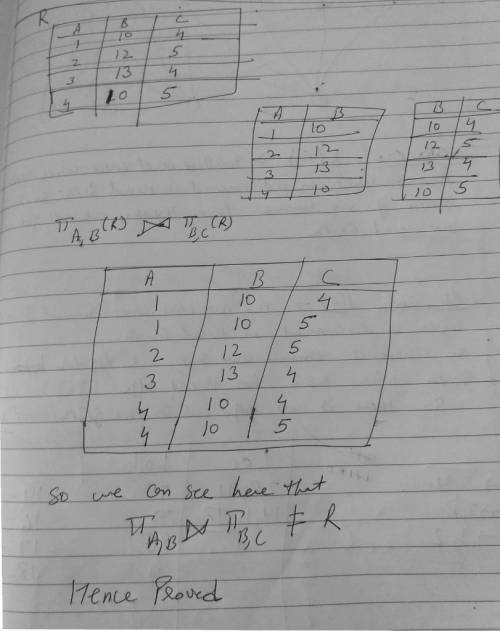
Suppose we have a relation schema R(A, B, C) with FD A rightarrow B. Suppose also that we decide to decompose this schema into S(A, B) and T(B, C). Give an example of an instance of relation R whose projection onto S and T and subsequent rejoining as in Section 3.4.1 does not yield the same relation instance. That is, pi_A, B(R) pi_B, C (R) notequalto R.

Answers: 2


Another question on Computers and Technology

Computers and Technology, 23.06.2019 02:30
People with high self-esteem: accept their strengths and weaknesses. believe that failed experiences are failures of their whole self. feel good about who they are only when they reach total success. need positive external experiences to counteract negative feelings that constantly plague them.
Answers: 1

Computers and Technology, 23.06.2019 14:30
Select the correct answer. andy received a potentially infected email that was advertising products. andy is at risk of which type of security threat? a. spoofing b. sniffing c. spamming d. phishing e. typo-squatting
Answers: 2


Computers and Technology, 23.06.2019 22:30
Apart from confidential information, what other information does nda to outline? ndas not only outline confidential information, but they also enable you to outline .
Answers: 1
You know the right answer?
Suppose we have a relation schema R(A, B, C) with FD A rightarrow B. Suppose also that we decide to...
Questions

Social Studies, 20.07.2019 04:50



Biology, 20.07.2019 04:50





History, 20.07.2019 04:50

History, 20.07.2019 04:50


Business, 20.07.2019 04:50



Mathematics, 20.07.2019 04:50

History, 20.07.2019 04:50

Biology, 20.07.2019 04:50


Social Studies, 20.07.2019 04:50

Biology, 20.07.2019 04:50