
Computers and Technology, 01.04.2020 03:14 deisyy101
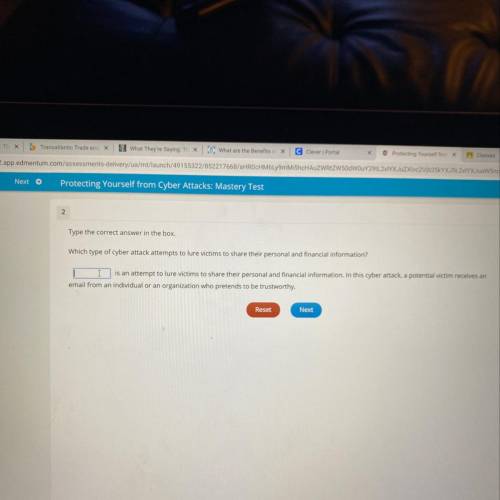
Which type of cyber attack attempts to lure victims to share their personal and financial information?

Answers: 3


Another question on Computers and Technology

Computers and Technology, 22.06.2019 07:30
An endless cycle of creation and response on the internet is called
Answers: 1

Computers and Technology, 23.06.2019 03:10
Acomputer has a two-level cache. suppose that 60% of the memory references hit on the first level cache, 35% hit on the second level, and 5% miss. the access times are 5 nsec, 15 nsec, and 60 nsec, respectively, where the times for the level 2 cache and memory start counting at the moment it is known that they are needed (e.g., a level 2 cache access does not even start until the level 1 cache miss occurs). what is the average access time?
Answers: 1

Computers and Technology, 23.06.2019 23:30
The keyboard usually has six rows of keys. which of the following is not one of the key group categories? letter keys number keys control keys graphic keys
Answers: 1

Computers and Technology, 23.06.2019 23:30
What are "open-loop" and "closed-loop" systems
Answers: 1
You know the right answer?
Which type of cyber attack attempts to lure victims to share their personal and financial informatio...
Questions

History, 28.07.2019 16:00

Physics, 28.07.2019 16:00


Mathematics, 28.07.2019 16:00


Chemistry, 28.07.2019 16:00

Biology, 28.07.2019 16:00

Mathematics, 28.07.2019 16:00

History, 28.07.2019 16:00



Spanish, 28.07.2019 16:00



Biology, 28.07.2019 16:00


Mathematics, 28.07.2019 16:10



Mathematics, 28.07.2019 16:10



