Computers and Technology, 30.03.2020 22:34 kcarstensen59070
You decide to begin your presentation by providing your audience an overview of networking, with an emphasis on security and why it is important for all company roles to assist in securing the company’s network. You decide to use the OSI model to explain the fundamental characteristics and components of networks because it is visual and presents the complexity of network communication in just 7 steps.
Include a discussion of each of the following in your response, being sure to emphasize the point(s) in the seven-layer OSI model where security is an issue, and listing specific security risks associated with each pain point:
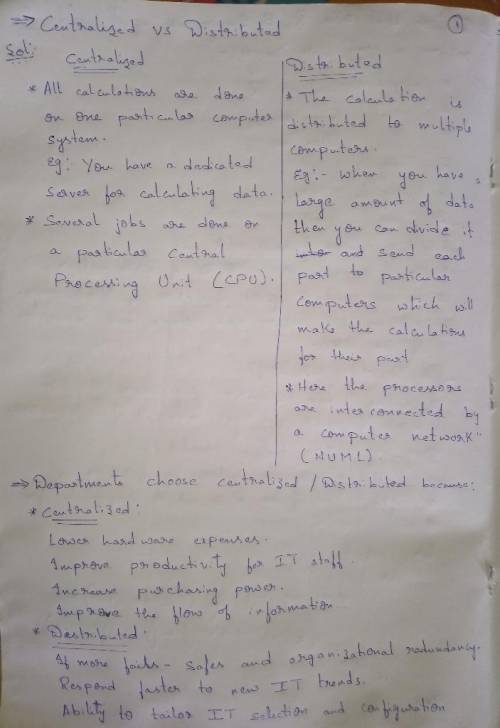
Distributed vs. centralized computer systems and why your department chose to be distributed/centralized
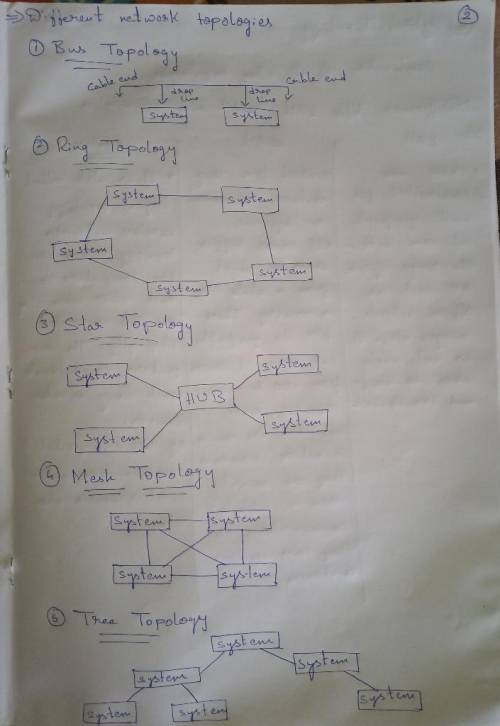
Different network topologies and why your department chose the topology it did
Why standards bodies are essential in networking and how your department complies with standards
The importance of communication protocols and which one(s) your department chose
The differences between LAN, WAN, and wireless technologies, and how your department incorporated each
The responsibilities associated with providing telecommunications services such as security, privacy, reliability, and performance
Next, you plan to describe basic routing and switching in the context of the OSI model (i. e., in which layer routing, switching, and cabling occur). To underscore your department’s commitment to achieving 24/7 availability, you describe some strategies your department follows to ensure the availability of network access in switched and routed networks.
Then, you describe at least three characteristics of an effective security policy, emphasizing the ways in which all departments in the company are responsible for helping secure the company network.
To reassure your audience of your network’s security, you list some strategies your department used to build security directly into the design of your company network.
Finally, malware has been in the news a lot lately, and you know you will be asked some questions about it. To answer them, you come up with a layperson-friendly definition of malware and identify at least two strategies your department has put into place for protecting your company’s network against malware.

Answers: 3


Another question on Computers and Technology

Computers and Technology, 21.06.2019 15:10
Match the terms in the hlookup syntax with their explanation. a. lookup value b. data table c. row index d. mode 1. name of the table that contains the value 2. specifies if an exact match must be found 3. value to be searched 4. name of the row that contains the value
Answers: 1

Computers and Technology, 23.06.2019 01:10
Are special combinations of keys that tell a computer to perform a command. keypads multi-keys combinations shortcuts
Answers: 1

Computers and Technology, 24.06.2019 10:00
(, urgent need): how do i change my username
Answers: 1

Computers and Technology, 24.06.2019 13:20
3. ranga ramasesh is the operations manager for a firm that is trying to decide which one of four countries it should research for possible outsourcing providers. the first step is to select a country based on cultural risk factors, which are critical to eventual business success with the provider. ranga has reviewed outsourcing provider directories and found that the four countries in the table that follows have an ample number of providers from which they can choose. to aid in the country selection step, he has enlisted the aid of a cultural expert, john wang, who has provided ratings of the various criteria in the table. the resulting ratings are on a 1 to 10 scale, where 1 is a low risk and 10 is a high risk. john has also determined six criteria weightins: trust, with a weight of 0.3; quality, with 0.2; religious, with 0.1; individualism, with 0.2; time, with 0.1; and uncertainity, with 0.1. using the factor-rating method, which country should ranga select? why? (2 points)
Answers: 3
You know the right answer?
You decide to begin your presentation by providing your audience an overview of networking, with an...
Questions

Mathematics, 28.01.2020 18:56


Mathematics, 28.01.2020 18:56



Health, 28.01.2020 18:56



Mathematics, 28.01.2020 18:56





English, 28.01.2020 18:56


Mathematics, 28.01.2020 18:56

Health, 28.01.2020 18:56

Health, 28.01.2020 18:56

Mathematics, 28.01.2020 18:56

Mathematics, 28.01.2020 18:56