Biology, 15.02.2020 02:09 gladyscasper44
An article in Information Security Technical Report, "Malicious Software—Past, Present and Future" (Vol. 9, 2004, pp. 6–18), provided the following data on the top 10 malicious software instances for 2002 (Fig. below). The clear leader in the number of registered incidences for the year 2002 was the Internet worm "Klez," and it is still one of the most widespread threats. This virus was first detected on October 26, 2001, and it has held the top spot among malicious software for the longest period in the history of virology. Suppose that 23 malicious software instances are reported. Assume that the malicious sources can be assumed to be independent. Round your answers to two decimal places (e. g. 98.76).
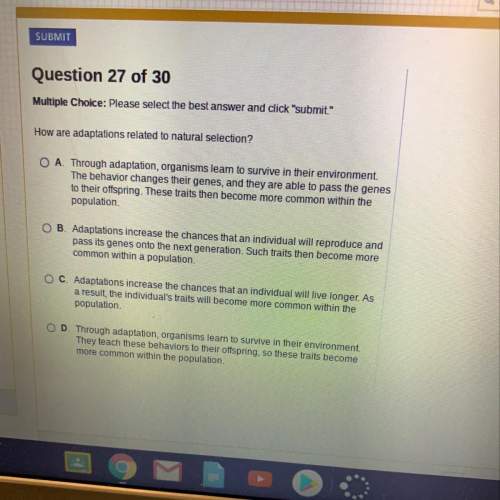
(a) What is the probability at least 4 instances are "Klez"?
(b) What is the probability that 4 or more instances are "Klez"?
(c) What is the mean and (d) standard deviation of the number of "Klez" instances among the 23 reported?

Answers: 3


Another question on Biology

Biology, 21.06.2019 23:00
Compare the depth of field when focusing with low power and high power. which power has the greater depth of field?
Answers: 1

Biology, 22.06.2019 02:00
Identify the terms using the following picture. principle of dominance item 1 can be described as the . item 2 can be described as the . the "p" represents from one parent.
Answers: 3

Biology, 22.06.2019 11:30
There are multiple lines of evidence that provide support for common ancestry and evolution. write 3-4 paragraphs describing at least three of them in detail. provide at least one example for each line of evidence.
Answers: 1

Biology, 22.06.2019 11:40
Which of the following happened during the precambrian era? the first prokaryotic cells the first eukaryotic cells development of photosynthesis all of the above
Answers: 1
You know the right answer?
An article in Information Security Technical Report, "Malicious Software—Past, Present and Future" (...
Questions




Mathematics, 21.11.2019 23:31



History, 21.11.2019 23:31